Latest Whitepapers

The Cost of ‘Good Enough’ Security ebook
Investing in cybersecurity technologies is one strategy for reducing cyber risk. But how can you be confident...
Drive Real Behaviour Change
Cybersecurity awareness training is one of the most important things you can do to secure your organisation....
5 Uncomfortable Truths About Phishing Defense
When over 90% of breaches start as phishing emails threats that email gateways miss and other defenses...
Bridging the Gap of Grief with Business-Driven Security
Worldwide spending on information security products and services will reach $86.4 billion in 2017, an...
A Guide for SMBs: Can I really become “less hackable”?
After nearly 20 years working in cybersecurity, I am still asked the age-old question by business owners:...
The Passwordless Future Report
Every company has to become a technology company in order to survive and thrive in today's competitive...
CRM Evolved Introducing the Era of Intelligent Engagement
Digital Transformation, a key focus of successful organizations, proves itself a business imperative,...
5 Steps Toward Cybersecurity Resilience for Government Agencies
Cybersecurity attacks continue to grow in number, in complexity and in impact. State and local government...
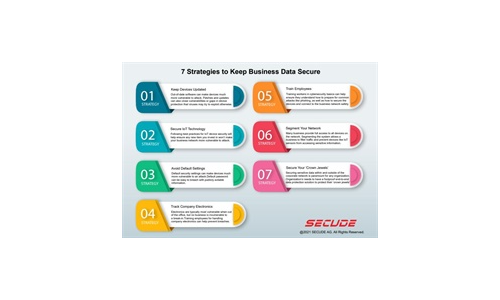
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
The Shared Responsibility Model Explained
In a cloud environment, your service provider takes on a share of many operational burdens, including...
Cloud Data Security 2023 Report by ESG, a division of TechTarget
…More than half (59%) of respondents believe that more than 30% of their organization's sensitive data...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.