Latest Whitepapers

5 Tips for Modernizing a Security Operations Center
When an organization decides to modernize a Security Operations Center (SOC) or implement a more formal...

2021 Norton Cyber Safety Insights Report Global Results
Prepared by the Harris Poll on behalf of NortonLifeLock, we consider: 1. Cybercrime: Incidence, Impact,...

Six Signs Your Email Gateway Might Need Replacing
Many organisations are spending way too much money on licensing the their email SPAM and malware gateway...
Cloud Security Report 2022
Cloud adoption continues to permeate throughout organizations as they embrace agile software development....

Forbes Study - CIO 2025
Important as the cloud already is, next-generation cloud and multicloud are expected to play even more...
12 Steps for Stronger Ransomware Protection
Over the last few years, we have signed up hundreds of MSPs. We like to ask every new customer why they...

The Future of Cybersecurity For Today’s Cloud- and Mobile-First World
Today, there's a sharp focus on embracing zero trust as the future of cybersecurity. With apps, users,...
6 Signs Your Email Gateway Might Need Replacing
Our experts have looked at the 6 signs your email gateway might need replacing. Read our guide and squeeze...
The Perimeter’s Gone. Can Your Security Handle It?
Organizations need to shift their security strategy to secure the new ways work gets done. That takes...
AI Driven Threat Defense The Next Frontier in Cybersecurity
It's undeniable that the landscape of modern cybersecurity has evolved dramatically—and at a rapid...
Navigating the Cloud: Key factors for long term success
The cloud is not only here to stay, its impact is growing. As cloud-based solutions and capabilities...

Brute Force: Guide to Mitigating Attacks
A brute force attack is when an attacker attempts to gain access to an environment by identifying valid...
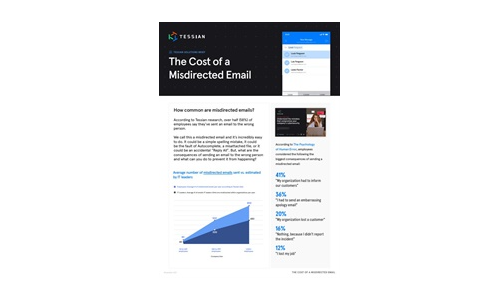
What is the Cost of a Misdirected Email?
The average number of misdirected emails is almost always higher than IT leaders estimate, making it...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.