Endpoint Protection
5 Steps Toward Cybersecurity Resilience for Government Agencies
Cybersecurity attacks continue to grow in number, in complexity and in impact. State and local government...
6-Step Cybersecurity Starter Guide for SMBs
Computers and the internet bring many benefits to small businesses, but this technology is not without...
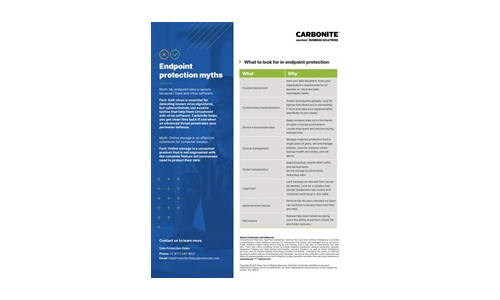
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...

Building the foundation of a mature threat hunting program
Many organizations, especially large global enterprises, don't always have the best visibility into how...
12 Steps for Stronger Ransomware Protection
Over the last few years, we have signed up hundreds of MSPs. We like to ask every new customer why they...
Building Your MSP Security Offerings
As a managed service provider (MSP), your customers already expect you to keep their networks secure....
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

