Endpoint Protection
The Perimeter’s Gone. Can Your Security Handle It?
Organizations need to shift their security strategy to secure the new ways work gets done. That takes...
Inside Complex Ransomware Operations and the Ransomware Economy
Ransomware operators have steadily become more sophisticated and more aligned with nation-state actors,...
Building Your MSP Security Offerings
As a managed service provider (MSP), your customers already expect you to keep their networks secure....
How to protect your business from ransomware
Read this guide to gain an insight into how you can take proactive steps to keep your company's files...
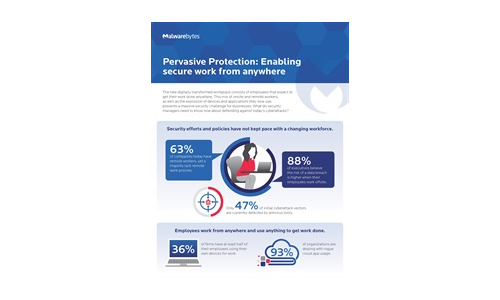
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....
The Complete Guide to Enterprise Ransomware Protection
The SentinelOne Complete Ransomware Guide will help you understand, plan for, respond to and protect...

Introducing a Cyber Security Service For Home WiFi
The renewal cycle for home WiFi routers is lengthy and involves users upgrading to a newer model once...

Realizing The Devops Vision In Embedded Systems
Markets demand ever more complex systems and faster development cycles. Meanwhile, there is a shortage...
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...
CMMC Compliance Guide
On January 1, 2020, the United States Department of Defense (DoD) released its Cybersecurity Maturity...
6-Step Cybersecurity Starter Guide for SMBs
Computers and the internet bring many benefits to small businesses, but this technology is not without...
Cyber Aware Infographic
Download this Infographic to see how you can protect yourself and your company from the risk of cyber-attack...
What Makes Real Threat Intelligence
First popularized in terminology several years ago, threat intelligence means many things to many people....
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.