Data Security
Bridging the Gap of Grief with Business-Driven Security
Worldwide spending on information security products and services will reach $86.4 billion in 2017, an...
Network Security Approaches and the Case for Zero Trust
Top executives say that legacy network technical baggage is holding them back from transforming their...
The edge advantage
Reduce costs and improve performance with edge computing. Read The edge advantage, and you'll understand...

The 10 Tenets of an Effective SASE Solution
As cloud adoption grows, cloud-enabled organizations are experiencing an influx of new security requirements....

PCI Compliance Best Practices
The Payment Card Industry Data Security Standard (PCI DSS) has been in place since 2004, with the latest...
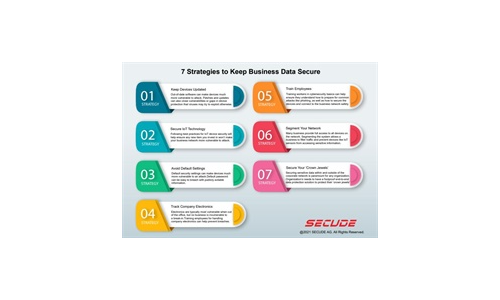
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
Building Your MSP Security Offerings
As a managed service provider (MSP), your customers already expect you to keep their networks secure....
Protect K-12 Schools from Cyberattacks with Active Breach Protection
Ransomware is not just another buzzword. It is a very real threat to educational institutions of all...

Cloud Adoption and Risk Report
The recent work from home mandate has dramatically changed how we live and work. Organisations are getting...

For digital sovereignty and transparency in the cloud
Shared use of infrastructure not only saves resources but also enables companies to push ahead with digitalisation...
Pain & Progress: Cybersecurity and Business Risk Study
Despite their best efforts and investments, some organisations still experience difficulty as a result...
The Top 10 Biggest and Boldest Insider Threats
Over the last two years alone, insider security incidents have jumped 47%, with the average cost per...

CIO Essential Guidance: CISO Security Threat landscape
After a year that saw the largest and fastest transformation in work patterns in history, security teams...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.